I published this on my LinkedIn page before the last presidential election (July 23, 2016), but I am re-posting it here because it examines both how visuals are distinct artifacts from the accompanying text and also how mixing propaganda (intentional misdirection or misinformation) with attempts to provide “real” or truthful information confuses the audience—an audience who will have to work very hard to separate fact from fiction. Reposting this seemed to be an appropriate follow-up to my previous blog entry, “Propaganda Files 1.”
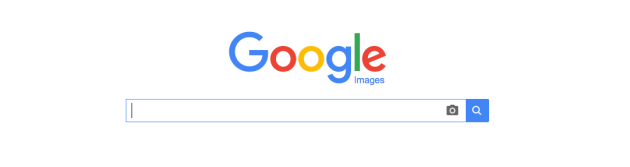
From the film Nineteen Eighty-Four 2005.
Since one of my primary professional concerns as a user advocate is how users see the information communicated to them, this article from the NYTimes.com Facebook feed grabbed my attention. The article’s author had analyzed Donald Trump’s acceptance speech for his nomination to be the candidate for President from the Republican Party. The article from the NYTimes online itself seems balanced and fair and generally keeps away from arguing a side, but instead, presents statistics that either would support or challenge Trump’s claims.
For the most part, the NYT article’s authors managed to state points clearly, keeping an informational tone. I believe that the article helps people who want further information to be able to research for themselves the various claims made in the speech, without too much interference by the author’s personal viewpoints. The references are there so that anyone who wants can fact-check the fact-checkers. My view is that an audience should examine all the issues to make informed decisions based on research done with an open mind. Whatever resources will aid people in that task are useful tools, as far as I am concerned.
Since writers, information designers, and graphic designers do not usually serve in the same job functions in organizations as large as the NYTimes, someone other than the author of the text of the article must have selected the image for the Facebook feed and edited the image for the newsfeed posting. The purpose of adding an image to the newsfeed is to grab the FB audience’s attention and get them to click through to the article, whereupon, the audience is encouraged to subscribe to the Times.
However, I just wanted to point out that the choice made in selecting the image to accompany the analytical article for the Facebook promotion (see image below) shows how VISUAL RHETORIC colors the impact of information for an audience.This all serves to show how—for the audience—reading and digesting the article rationally is one thing, but being subliminally persuaded via the accompanying images, is quite another one.

Image by Josh Haner ©2016 The New York Times
The selection of an image showing a giant screen view of Donald Trump pulls out of our subconscious every thing we have ever heard concerning the phrase, “Big Brother is Watching You,” from George Orwell’s dystopian novel, 1984, and in fact, the image chosen for the NYT’s Facebook blurb is highly reminiscent of the MGM movie version of that book; the movie was released in the year 1984 and it starred Richard Burton and John Hurt (see image at top of post). [This movie is rated for adults because of some sexual content (R).] I recommend the movie and, most especially, I recommend Orwell’s book. Everyone should read the book, 1984. The book shows a world in which persuasion has become coercion on every level, backed by the powerful arm of a state that has stripped the populace of any individuality, conscience, privacy, or civil liberties.
Whatever you think of Trump, I wanted to point out the subtle (or not so subtle) use of images on this Facebook newsfeed blurb that attempt to subliminally persuade you that Donald Trump is going to institute a regime similar to what is found in Orwell’s terrifying vision of the future.
In my opinion, the text of the article does a very good job of showing from a rational standpoint some reasons to question Mr. Trump and his candidacy. However, the image used to accompany the newsfeed makes an emotional (non-reasoning) argument in order to awaken doubts about the candidate without having to back them up with facts–just like Mr. Trump’s speech.
For example, the way that Trump uses fear and exaggeration to paint a picture of a dire situation—that only he sees and only he can fix—is truly a misuse of facts and stretching of the truth to convince people to vote FOR him. How ironic that the visual rhetorician placing and choosing the image for the Facebook feed uses the same tactics, fear and exaggeration, to convince you to vote AGAINST him. Since I can’t know the motivation of whoever chose the image or the photographer for the photo used in the Facebook blurb, I, of course, can’t know definitively why that particular photo was selected. I can see the name of the photographer (Image by Josh Haner/The New York Times) captioning a video article, with the title, “Trump Speech Casts US in Dark Light,” about halfway down the page on the NYTOnline article. *
However, professionals don’t just randomly place images on a page. The photo on the Facebook newsfeed blurb was not the image featured in the article. Rather, the NYTimes.com article featured a normal-sized image of Trump at the podium, just like any candidate ready to start a speech. Obviously, this particular large-scale image of the hall, with Trump at the podium, surrounded by masses of people, with the backdrop of a giant-screen close-up of his face, must have been selected over innumerable other possibilities. The obvious connection made is that Donald Trump is just like Orwell’s powerful party leader, riding the wave of a cult of personality, like those of “the party” in Orwell’s book. Whether this is true or not is not my point. Of course, if the photo of Trump in a hall with giant screens of his face was taken, it must be true that he actually appeared like that in real life. However, the selection of that particular shot at that particular moment to represent that particular text is completely a rhetorical and persuasive choice made by someone involved in the process who is not the same person who wrote the article or even the same person who chose the page shots for the online newsfeed or presumably, the hard copy newspaper.
My point is that we as the audience for information need to be aware that images are being used rhetorically in communications and the information we receive can be twisted around by the visuals framing it (see my post on “Framing“).
Images are powerful, persuasive tools that often work their persuasion on the edges of our conscious mind. I would have us be aware of what is being said to us, even in our unconscious minds, so that we are fully informed, and able to pose reasoned arguments and refute those we disagree with rationally, rather than posing and refuting strictly by emotional means.
By paying attention to and questioning what you see, you can bring what is not noticed more fully into the purview of your reasoning skills to give you more control of the messages that you receive, believe, and send to others.
* Listening to this video and reading this article again is very, very interesting from the vantage point of nearly two years into the future, since the talking points in Trump’s speech can be analyzed from our current vantage point for truth and perspective; I would encourage everyone to do just that.
For Further Information:
Read the NYTimes article here:
“Fact Checking the Truth That Donald Trump Has Promised”
Buy the book 1984:

Click here to buy the book 1984 by George Orwell in paperback on Amazon.
References Cited:
Orwell, George (1949). Nineteen Eighty-Four. A novel. Signet.
Radford, Michael, John Hurt, and Richard Burton. Nineteen Eighty-Four. 2005.
Shear, Michael D, and Nick Corasaniti. “Fact-Checking the Truth That Donald Trump Promised.” The New York Times, The New York Times, 21 July 2016, http://www.nytimes.com/2016/07/22/us/politics/donald-trump-fact-check.html.







 Piraro, Daniel. “Bizarro Comic Strip for February 01, 2016.” Comics Kingdom. N.p., n.d. Web. 1 Feb. 2016. <
Piraro, Daniel. “Bizarro Comic Strip for February 01, 2016.” Comics Kingdom. N.p., n.d. Web. 1 Feb. 2016. <